North Korean hackers stole £300m in cryptocurrency last year, report finds
The UN accuses Pyongyang of spending stolen funds on nuclear and ballistic missiles programmes

North Korean hackers stole about £300m in cryptocurrency in 2021, making it one of their most lucrative years on record, a new report has suggested.
Blockchain analysis company Chainalysis said it is likely that the Lazarus Group, an infamous state-sponsored cybercrime unit, was behind most of the seven digital attacks, three more than the total number identified over the preceding 12 months.
The country generated 40 per cent more money from hacking last year than it did in 2020, according the report by Chainalysis.
“Once North Korea gained custody of the funds, they began a careful laundering process to cover up and cash out,” its report said.
Although the firm did not name all the organisations targeted by Pyongyang, it found that the majority were investment firms and exchanges, including the cryptocurrency trading platform Liquid.com.
Researchers at Chainalysis also discovered £125m in unlaundered digital currency that had been stolen by the hackers from 2017 to 2021.
The report said that North Korea might be keeping these funds to buy themselves time while trying to outfox law agencies.
“Whatever the reason may be, the length of time that [North Korea] is willing to hold on to these funds is illuminating, because it suggests a careful plan, not a desperate and hasty one,” Chainalysis added.
The UN has accused Pyongyang of spending its ill-gotten gains on its nuclear and ballistic missile programmes as a way of circumventing sanctions. North Korea has denied involvement in any illicit hacking activities.
In 2019, the UN Security Council said that North Korea had earned roughly £1.5bn over three years in illegal cyber activities.
In one of its most famous cyberattacks, North Korea is believed to have targeted Sony Pictures Entertainment in 2014, after the studio released a film showing the assassination of the country’s leader.
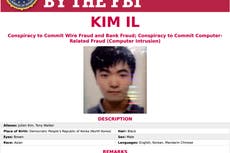
Three North Korean men were charged by the US Department of Justice in 2021 over attempts to steal about £1bn in cash and cryptocurrency.
“The scope of the criminal conduct by the North Korean hackers was extensive and long-running, and the range of crimes they have committed is staggering,” said US attorney Tracy Wilkinson at the time.
The group, who allegedly worked for the state’s Reconnaissance General Bureau, also allegedly attacked the NHS in 2017 with “WannaCry 2.0” ransomware.
Agencies have contributed to this report
Join our commenting forum
Join thought-provoking conversations, follow other Independent readers and see their replies
Comments

Bookmark popover
Removed from bookmarks