iPhone passwords 'shockingly easy' to steal from iOS users
'Even users who know a lot about technology have a hard time detecting that those alerts are phishing attacks'
A developer has demonstrated how “shockingly easy” it is to steal people’s Apple ID passwords.
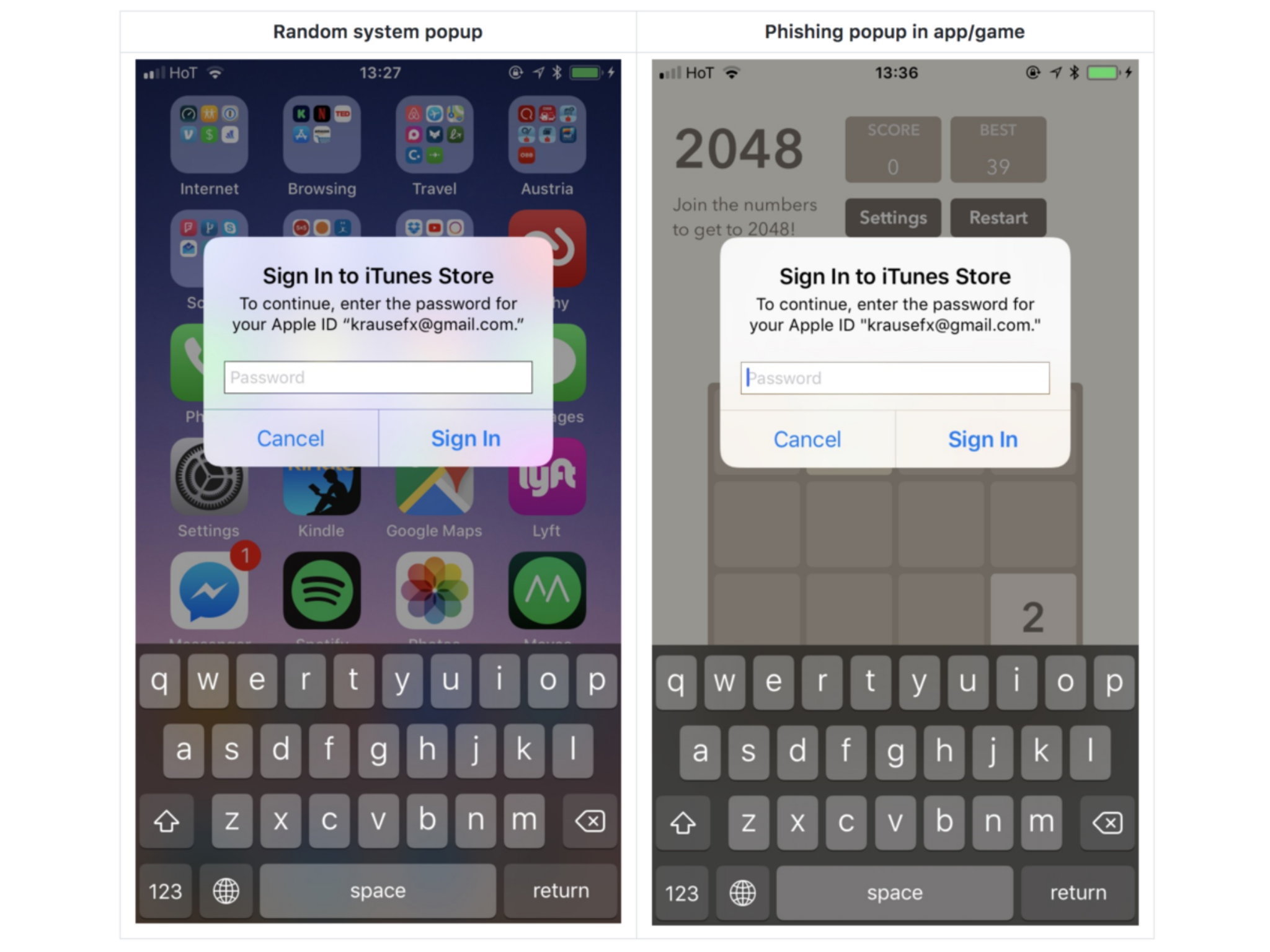
Felix Krause created a proof of concept phishing attack that looks identical to the official system popups in iOS.
He says it’s possible for criminals to programme apps to run certain code only after Apple has approved it for a spot in the App Store, and that the scheme works because iOS has “trained” users to automatically enter their details without questioning a popup's legitimacy.
Mr Krause says he was able to create the lookalike popup with less than 30 lines of code, and that “every iOS engineer” would be capable of creating their own phishing code.
“iOS asks the user for their iTunes password for many reasons, the most common ones are recently installed iOS operating system updates, or iOS apps that are stuck during installation,” he wrote in a blog post.
“As a result, users are trained to just enter their Apple ID password whenever iOS prompts you to do so. However, those popups are not only shown on the lock screen, and the home screen, but also inside random apps, e.g. when they want to access iCloud, GameCenter or In-App-Purchases.
“This could easily be abused by any app, just by showing an UIAlertController, that looks exactly like the system dialog. Even users who know a lot about technology have a hard time detecting that those alerts are phishing attacks.”
It highlights a huge potential danger for users, who could easily be tricked into simply handing their login details to a cyber criminal.
Mr Krause recommends hitting the home button when any popup appears in iOS. If doing so makes both the app and the popup disappear, it was a phishing attack, he says.
He says you can protect yourself further by dismissing popups altogether and instead only enter your password information in the Settings app.
“This is the same concept [as never clicking] on links on emails, but instead open the website manually,” he wrote.
Join our commenting forum
Join thought-provoking conversations, follow other Independent readers and see their replies
Comments
Bookmark popover
Removed from bookmarks