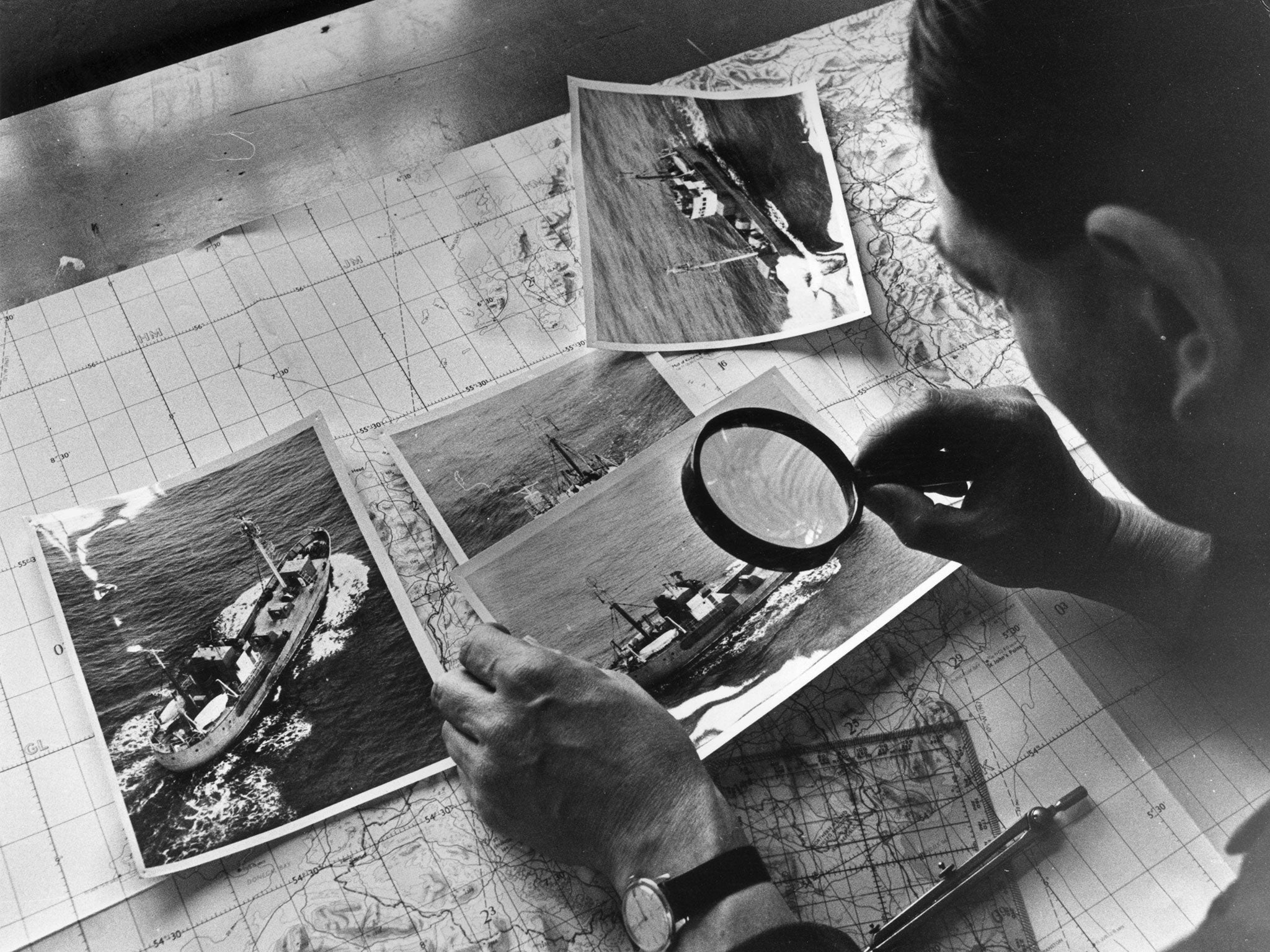
Caught in the crossfire of a cyber Cold War
Fears are mounting that Vladimir Putin has instructed hackers to target banks like JP Morgan
A few weeks ago, America’s biggest bank was hacked. Nimble computer whizzes scaled JP Morgan’s complex digital ramparts and found themselves sitting at the heart of a US institution with assets worth $2.5 trillion. Several gigabytes of data were taken, though the bank insists it has not yet seen unusual levels of fraud.
The FBI is investigating the attack, revealed yesterday, with at least one other bank reportedly affected.
Hacking is nothing new for a company of JP Morgan’s size. As Dave Palmer, head of technology at the cyber security firm Darktrace, put it: “Being an organisation on the internet is like having someone constantly banging on your door and rattling your windows.”
But what made this attack different, investigators believe, was the possible identity of the perpetrator: the Russian state.
The sophistication, origin and target have led experts to conclude that the incursion may have been the work of hackers either directly instructed or at least supported by Vladimir Putin’s Government, with speculation that it could be in retaliation for the West’s involvement in Ukraine. It is not the first time Russia has been accused of using such tactics: Georgia and Estonia both faced cyber attacks during periods of conflict with Russia.
But the prospect of Western businesses coming under attack not only from cyber bandits but hostile nations is a worrying one. The Sun newspaper, Microsoft and eBay have all already been targeted by the Syrian Electronic Army, while five Chinese military officers were indicted in the US earlier this year on corporate hacking charges.
In July, the Chinese businessman Su Bin was arrested for allegedly hacking into Boeing and other defence contractors’ IT systems in an attempt to obtain information on jets, military cargo, aircraft and weapons to sell to Chinese companies.
“Right now there is a huge cold war happening on the internet,” said Costin Raiu, director of global research and analysis at the cyber security firm Kaspersky Lab. “In such an environment, where nation states are fighting each other, businesses are in danger of becoming collateral damage.”
Details on the JP Morgan attack are scant but Joe Hancock, a cyber-security expert at the insurer Aegis, said: “State-sponsored attackers tend to be looking for economically sensitive data, intellectual property and things that are more directly useful to the country.”
State-sponsored or endorsed cyber attacks are nothing new, with the earliest example dating back to 1998. But Mr Raiu said incidents have exploded since the detection in 2010 of Stuxnet, a computer worm that infected Iran’s nuclear systems and was believed to have been created by the US and Israel. The American oil giant Chevron suffered collateral damage in that attack after its computers were infected with the virus.
Mr Raiu estimates that there are now between 100 and 1,000 state-backed cyber attacks annually, but certainty is elusive. “Attribution is nearly impossible,” said Mr Palmer. “It’s easy for someone with knowledge and resources to make it look like it was someone else.”
Much of what security experts believe to be state-backed hacking has in essence been cyber espionage. But there is a danger of it escalating. “What we worry about most is someone being able to carry out a real-world action based on a cyber attack – being able to cause a problem with the electricity grid or stopping a business being able to function,” said Mr Hancock.
Sources indicate that the JP Morgan attack was isolated to its US operations, but the UK is just as vulnerable and several big European banks have reportedly been targeted in recent months. Cyber security is one of the Bank of England’s biggest priorities – it has already run two “war game” scenarios with lenders to test defences and has put in place a cross-company network for reporting attacks. In June the Bank also introduced CBEST, a framework for assessing cyber risk.
At the moment, much of the focus is on detection rather than protection, in part because of the difficulty stopping state-backed attacks. The JP Morgan breach used a so-called “zero day vulnerability” – a flaw in a system that had not yet been discovered. Mr Hancock said: “There’s always a way to get into any organisation if you have enough money and enough time, which ultimately state-sponsored efforts have.”
However, Mr Palmer stressed that state-backed hacks still only represent a “tiny fraction of a per cent” of total attacks, many of which are amateurish and easy to thwart. Businesses are advised to use “ethical hackers” to test for vulnerabilities before criminals spot them.
But Mr Hancock warned: We are seeing an uptick in cyber attacks across all industries.” He added: “There’s a quote from Robert Mueller [head of the FBI at the time] from 2012: ‘There are two types of businesses – those who have been hacked and those who will be.’”
Infected: How hackers got in
2014: ‘Energetic Bear’ US and European energy companies were infected by malware that allows energy monitoring and possibly interference with real-world networks. The attack was believed to be Russian.
2014: ‘Snake’ Ukrainian computers, including those of the Kiev Government, were hit by a virus, allowing surveillance and the launching of more destructive attacks. Russia thought to be behind the attack.
2013: ‘Syrian Electronic Army’ The SEA targeted a series of high-profile websites, such as The New York Times, Twitter and the US Marine Corps, taking over the sites and posting pro-Syrian messages.
2012: ‘Izz ad-Din al-Qassam Cyber Fighters’ Hackers suspected of having links to Iran targeted the websites of US financial institutions such as Bank of America and the New York Stock Exchange.
Join our commenting forum
Join thought-provoking conversations, follow other Independent readers and see their replies
Comments
Bookmark popover
Removed from bookmarks