Isis losing ground in online war against hackers after Westminster attack turns focus on internet propaganda
Anti-Isis activists warn they are 'playing whack-a-mole' as Isis fights back with new sites and accounts

“Owned again! Your site is ours Daesh. You have nowhere to hide. You are weak,” reads a message by hackers waging war on Isis’ online “caliphate”.
They are celebrating a huge cyber attack that sees anyone attempting to view the terrorist group’s Amaq propaganda website met with malicious software disguised as an update.
By creating a virtual “back door” into devices, it is able to activate cameras, log keystrokes, steal files, read phone messages, take screenshots, detect GPS locations and collect contacts from unsuspecting jihadis.
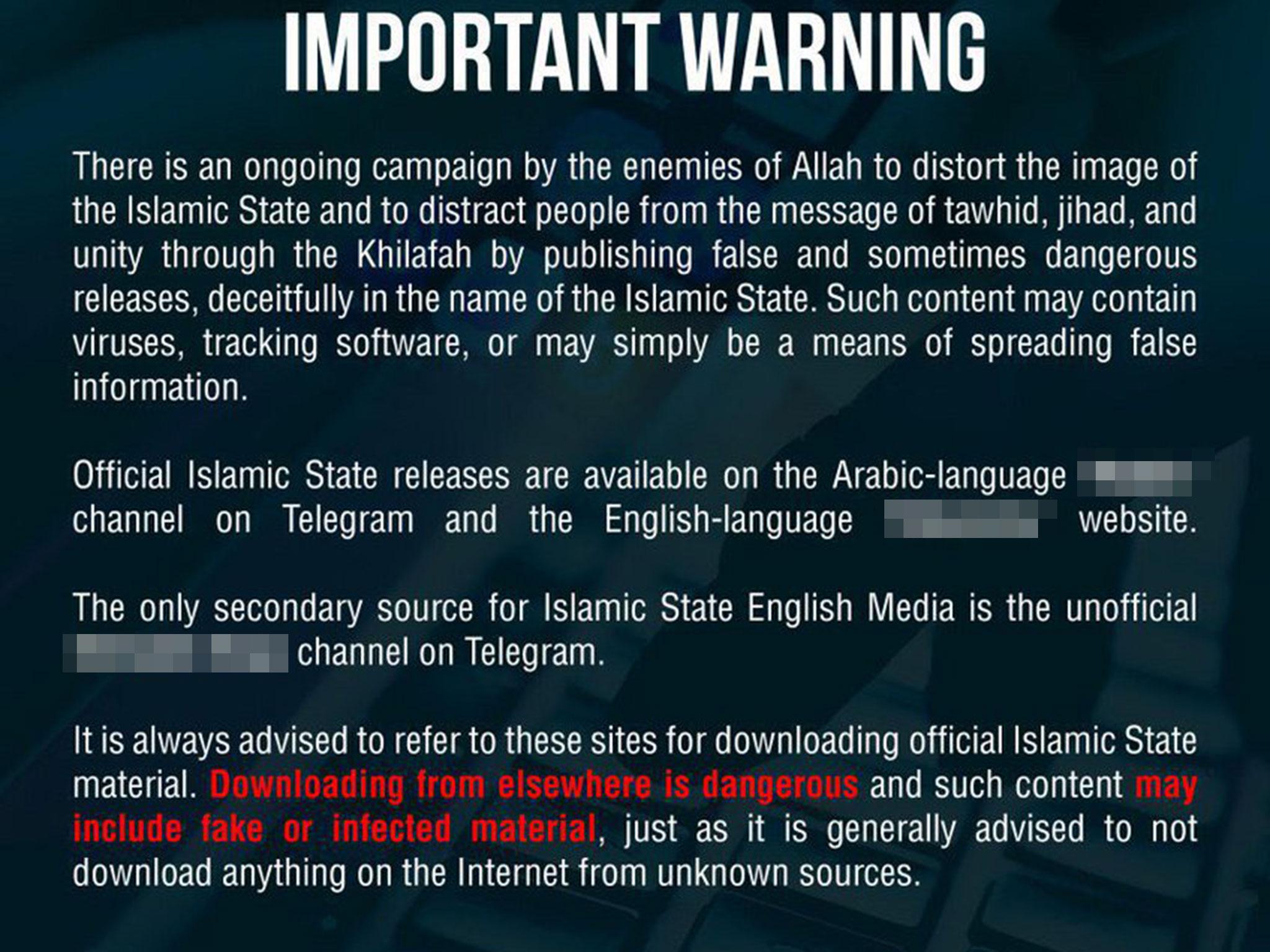
The infiltration forced Isis to issue a warning to followers through Amaq’s encrypted Telegram channel, saying its latest Arabic language website had been “penetrated” by a virus, adding: “Please exercise caution.”
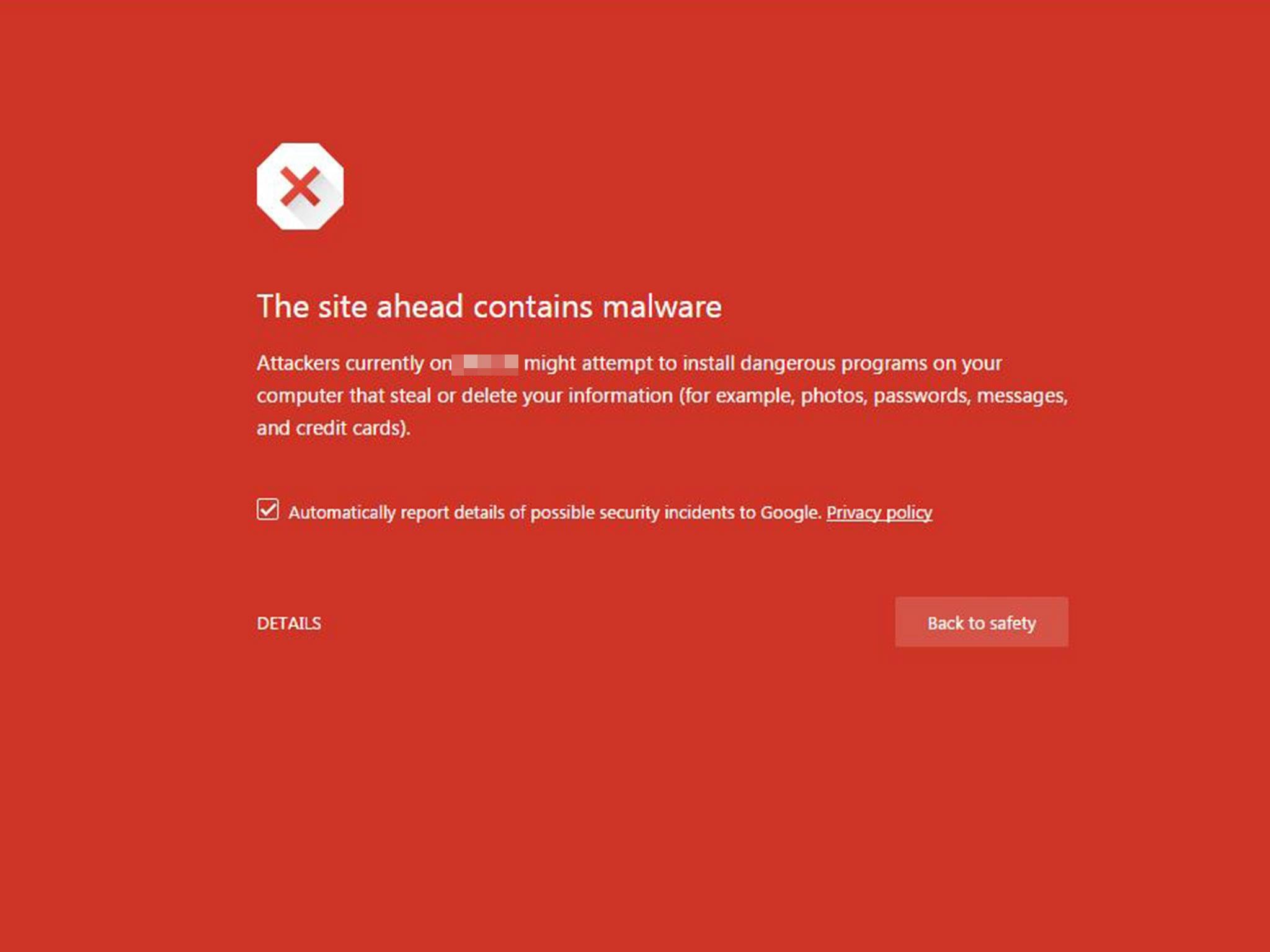
When The Independent tried to access the site, it was automatically blocked with a warning from Google that attackers “might attempt to install dangerous programs on your computer that steal or delete your information” including photos, passwords and credit cards.
It is the latest move to ensnare Isis supporters through the group’s own propaganda, with a fake version of its Android mobile app previously created to track extremists and convincing forgeries of a propaganda magazine released online.
Charlie Winter, a senior research fellow at the International Centre for the Study of Radicalisation and Political Violence (ICSR), said extremists were becoming “agitated” by intensifying online attacks.
“It’s leaving a lot of Isis paranoid and it’s a joy to behold,” he told The Independent.
“Something’s afoot. Someone is putting a lot of effort in sowing discord and paranoia – it’s very effective.”
Hackers around the world are launching ever more sophisticated attacks on Isis’ websites and communications, with collectives hailing their success using the hashtags #OpIsis and #OpIceIsis on Twitter.
Among them is CtrlSec, which has declared its mission to limit and destroy “online extremism in all shapes”.
Its founder is Mikro, a 20-something hacktivist leading global efforts to get jihadi Twitter accounts taken down.
“Isis is the main target but we handle all types of extremists,” he told The Independent.
“They adapt to the situation they are put in, like any other person would over time.”
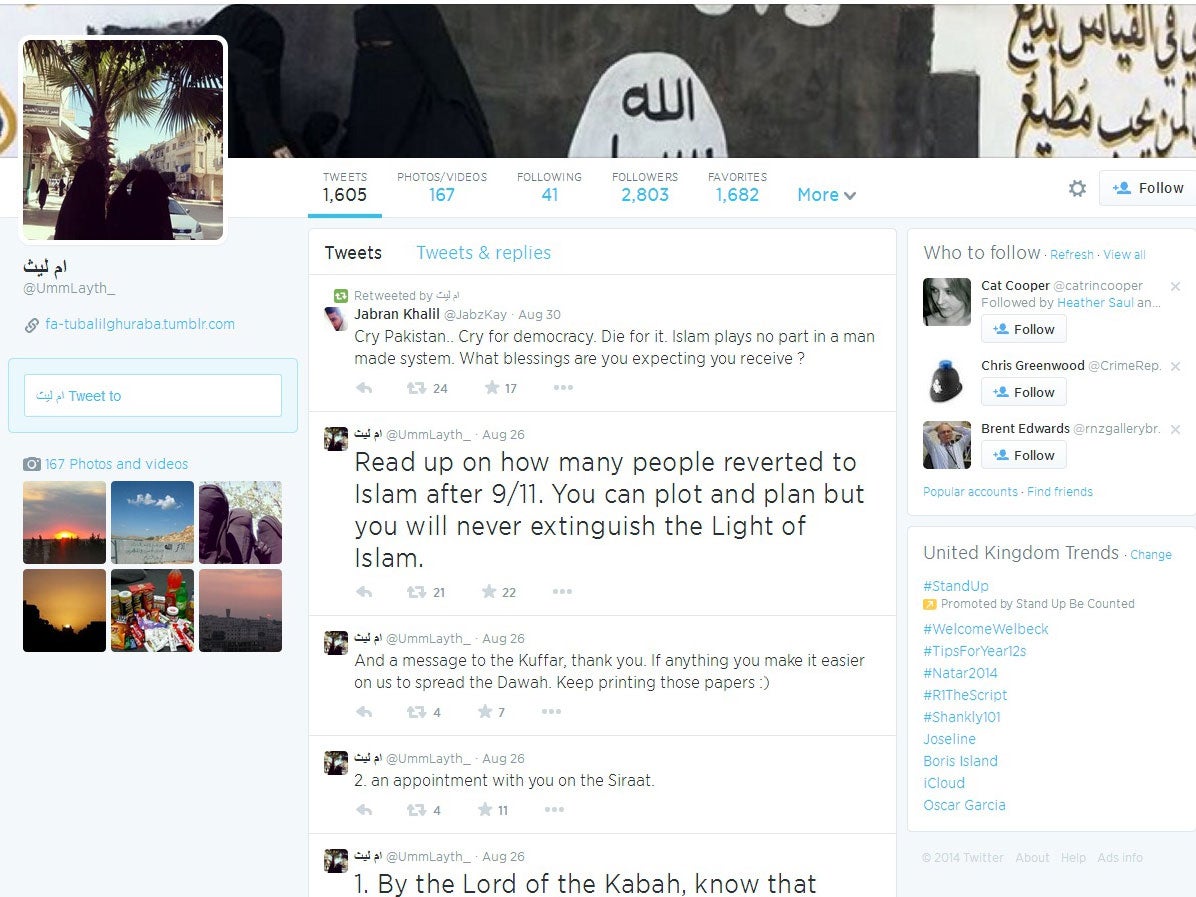
When the “caliphate” was declared three years ago, militants were openly using Twitter to call for people to travel to Syria or Iraq, while sharing gory videos alongside rosy depictions of their lives in the so-called Islamic State.
So brazen were communications that in 2015, Mikro and fellow hacktivists chanced upon an Isis cell in Tunisia plotting attacks on British and Jewish tourists and passed the information to security services, resulting in more than a dozen arrests.
The accounts of Isis’ most prolific tweeters have long been removed but supporters and “fanboys” continue to start countless new accounts in running battles to evade activists and moderators.
Mikro believes technology firms and governments are not doing enough to crack down on extremist social networking, claiming activists’ efforts are more effective.
“The day we run out of work then enough is done, but I do not see an end to this in sight,” he added.
“We are playing whack-a-mole since third parties don’t collaborate.”
Mikro said he has received so many death threats that he stopped bothering to record them two years ago, and keeps his name, identity and location a closely guarded secret for his own safety.
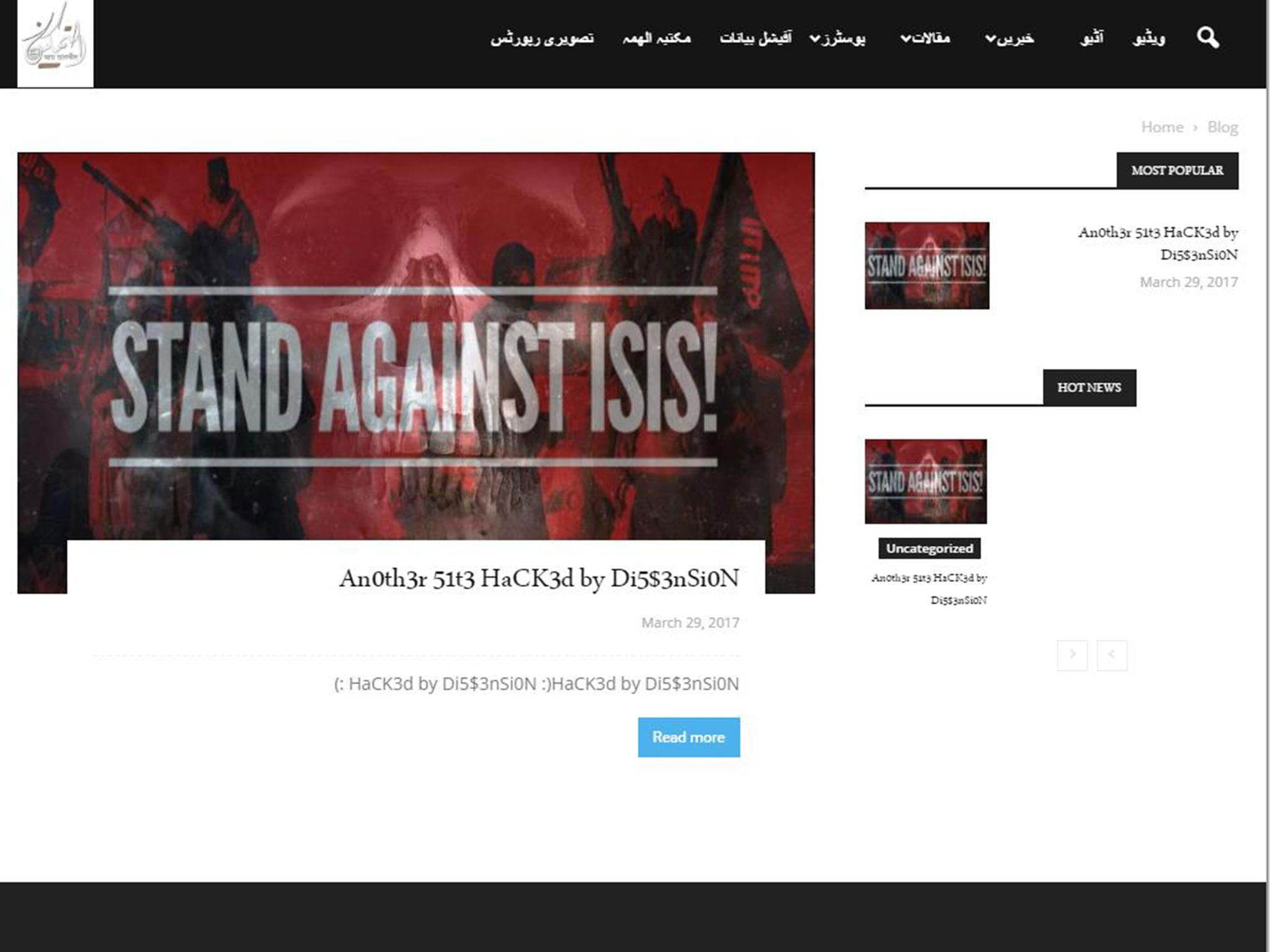
Similarly secretive is a Muslim collective called Di5s3nSi0N, which has been hacking websites hosting Isis propaganda including its Amaq and Halummu news agencies, al-Furqan video outlet and al-Bayan online radio station.
It overwrites sites with its calling card – a red and black picture with the caption “Stand Against Isis” and the message “HaCK3d by Di5s3nSi0N”, accompanied by smiley faces.
The group identifies itself as Sunni Muslim, with a mission statement reading: “The steadfast youth of ahlus-Sunnah wal-Jammah can no longer tolerate the obscenities of the Baghdadi gang who abuse religion and insult the dignity of people.”
It sends out frequent tweets aiming to enrage Isis supporters, telling them they are “soooooo weak” and “you are not Muslim”, warning: “We’re coming for you.”
Meanwhile, the End of Daesh group describes itself as the “online nemesis of Isis”, calling for help to “smash” extremist sites with cyber attacks.
Members of the Anonymous hacking collectivist are also continuing their own #OpIsis attacks after declaring war on the group following the Charlie Hebdo massacre.
Gregg Housh, a former Anonymous activist, said hackers were using a range of methods including distributed denial-of-service (DDoS) attacks that flood websites with traffic until they crash, to great effect.
“I think the hacktivists are winning the battle for one very simple reason,” he told The Independent.
“When you have to move, your user base has to find the new sites and accounts.
“It’s hard to build a large following and a large amount of influence if you have to keep jumping around to new domains, new hosts and new Twitter accounts.”
But Mr Winter warned that Isis is continually adapting to spread its message, even as it loses swathes of territory around its most symbolic strongholds in Syria and Iraq.
“Certainly the landscape has changed profoundly over the course of the past few years, but the group is still eminently capable in propaganda dissemination,” he said.
“A website gets knocked down and it comes back exactly the same in a few days or hours with a slightly different url…it’s a game of cat and mouse.”
Mr Winter said that although it had become more difficult for Isis to circulate its propaganda and posts do not stay online for as long as they once did, the group is still publishing huge amounts of articles, magazines, videos, photos and audio files.
“No matter how inhospitable the environment is, they’re still going to be able to use the internet,” he added, warning of far-right websites republishing Isis material that remains “very easy to access”.
Mr Winter said: “Islamphobes are circulating propaganda more efficiently than Isis itself can ever do, we need to start having that conversation.”
The Westminster attack has once again turned the British Government’s focus on to the group’s online propaganda efforts after Isis claimed responsibility for the massacre the left four victims dead.
Revelations that Khalid Masood used the messaging service WhatsApp just minutes before launching his attack sparked fresh debate over encryption and privacy, with communications providers meeting the Home Secretary on Thursday.
Amber Rudd said that although progress has been made, she would “like to see the industry to go further and faster in not only removing online terrorist content but stopping it going up in the first place”.
“I’d also like to see more support for smaller and emerging platforms to do this as well, so they can no longer be seen as an alternative shop floor by those who want to do us harm,” technology firms were told.

Michael S Smith II, a terrorism expert who recently gave evidence at the Global Coalition conference hosted by the Foreign Office, agrees, arguing that companies need to “increase the risk of exploiting their technologies to recruit and incite violence”.
“There’s really only so much that the UK government can do apart from diplomacy,” he added.
“Propaganda is merely one factor in the larger set of problems when you look at Isis’ unprecedented recruitment and incitement capabilities.”
He warned that Isis was using social media not only to spread its message, but to incite and control attacks, including a 2015 shooting at an exhibit featuring cartoons of the Prophet Mohamed in Texas.
That was linked to British Isis hacker Junaid Hussain, who foreshadowed attack on Twitter after the perpetrators used the social network to pledge allegiance to Abu Bakr al-Baghdadi.
Mr Smith argued that Western governments had been left behind by Isis’ exploitation of technology created in their own countries, with the group issuing detailed advice on how to encrypt communications and evade detection.
He called for more efforts to disrupt the publication of extremist material, warning that once it was flagged and removed, it was “too late” to stop countless copies popping up elsewhere.
“When you see all these hactivist groups forming, Isis has succeeded in undermining confidence in our governments’ capability to manage threats emanating from the cyber domain,” he added.
The British Government’s Counter Terrorism Internet Referral Unit, which searches for extremist material and works with internet companies to take it down, has helped remove 250,000 pieces of extremist content since 2010, working at a current rate of 2,000 per week.
Join our commenting forum
Join thought-provoking conversations, follow other Independent readers and see their replies
Comments
Bookmark popover
Removed from bookmarks