Nude celebrity photo hacks the work of an 'underground nude trading ring', reports claim
Numerous anonymous posters on forums where the images first surfaced say the cache of images has existed for 'months' and that more leaks are coming

Following the release of scores of nude photographs of celebrities including Jennifer Lawrence and Kate Upton, reports of an “underground celeb n00d-trading ring” suggest that the images are not simply the product of lone hacker.
Since the first batch of stolen photos was posted online on Sunday evening, new releases have trickled out over the course of the week.
Posters on anonymous image-sharing boards 4chan and AnonIB claim that the cache of stolen images was assembled by a group of hackers and took “several months of long and hard work by all involved”.
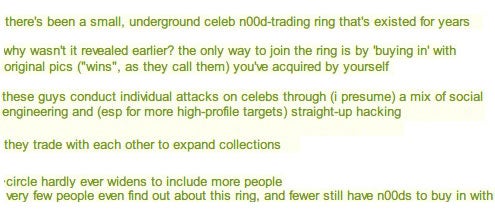
Another poster on 4chan has claimed that an “underground celeb n00d-trading ring” that finds these images has “existed for years," with individuals conducting trades with another to “expand [their] collections”.
“These guys conduct individual attacks on celebs through (I presume) a mix of social engineering and (esp for more high-profile targets) straight-up hacking,” wrote the anonymous tipster. “The only way to join the ring is by ‘buying in’ with original pics (“wins”, as they call them) you’ve acquired by yourself.
“[The] circle hardly ever widens to include more people – very few people even find out about this ring, and fewer still have n00ds to buy in with.”
The poster suggested that one “self-style ‘rich kid’” bought into the trading ring and then “blew the lid on this whole operation by sharing them with outsiders for the first time”. This inspired others to “[come] out of the woodwork offering up some of their collections for donations," leading to the avalanche of images on Sunday evening.
Speaking to The Independent, David Emm, a senior researcher at Kaspersky Lab, said that the theory was "certainly feasible" and that the motivation for hacking a celebrity was rarely the same as the motivation for hacking a member of the public.
"If someone wants to hack my Facebook the probability is they're not looking at pictures of me but they're looking to spread malware. But for a well-known person or actor or actress there's juicy information that can be found and, of course, the sleaze factor of getting access to private pictures."
Although first-hand anonymous reports like this are impossible to verify, this particular story fits with other fragments of information about what some publications are referring to as ‘celebgate’.
Sports website Deadspin claims that they heard about the existence of a large cache of images several weeks ago thanks to a tipster. “These photos appear to have been floating somewhere in the bowels of the internet one way or another for awhile,” writes Samer Kalaf. “We tried contacting our original tipster today with no response."
The theory of a collection gathered over time also fits the wide scope of dates attached to the photos, but the existence of multiple hackers - and subsequently of multiple leakers - makes it impossible to identify what Deadspin referred to as “Pervert Zero” – an original hacker.
One individual who posted the images online was identified by 4chan and Reddit users after including identifying information in screenshots used to boast of his collection. He later told Buzzfeed that he was simply a leaker, and that “the real guy is on 4chan posting intermittently.”
Mr Emm confirmed that any hackers involved were far more likely to be keeping as quiet as possible right now. "The likelihood is that these people always wanted to do it surreptitiously. They wouldn't be hacking accounts and splurging it everywhere - that's the last thing they'd do."
A report from Business Insider suggests that the iCloud hacks (this is Apple’s digital back-up service that uploads iPhone images to online servers automatically) are regularly traded online, with hackers either using specialized software or simply abusing iCloud’s iForgot password reset tool to gain access to celebrities’ accounts.
Security experts’ theories on how the hackers gained access to the private photographs echo this version of events. (The advice to worried iCloud users is make sure they have a strong, unique password for their account and to turn on two-step verification to be doubly safe).
At the moment all of this is speculation, but with the FBI and Apple confirming that they are actively investigating the issue we can certainly expect to hear more about the existence – or non-existence – of an “underground celeb n00d-trading ring” over the coming weeks.
Join our commenting forum
Join thought-provoking conversations, follow other Independent readers and see their replies
Comments
Bookmark popover
Removed from bookmarks